Cybersecurity and Information Data Protection
PROGRAM
Cybersecurity and Information Data Protection
PROGRAM
Cybersecurity and Information Data Protection
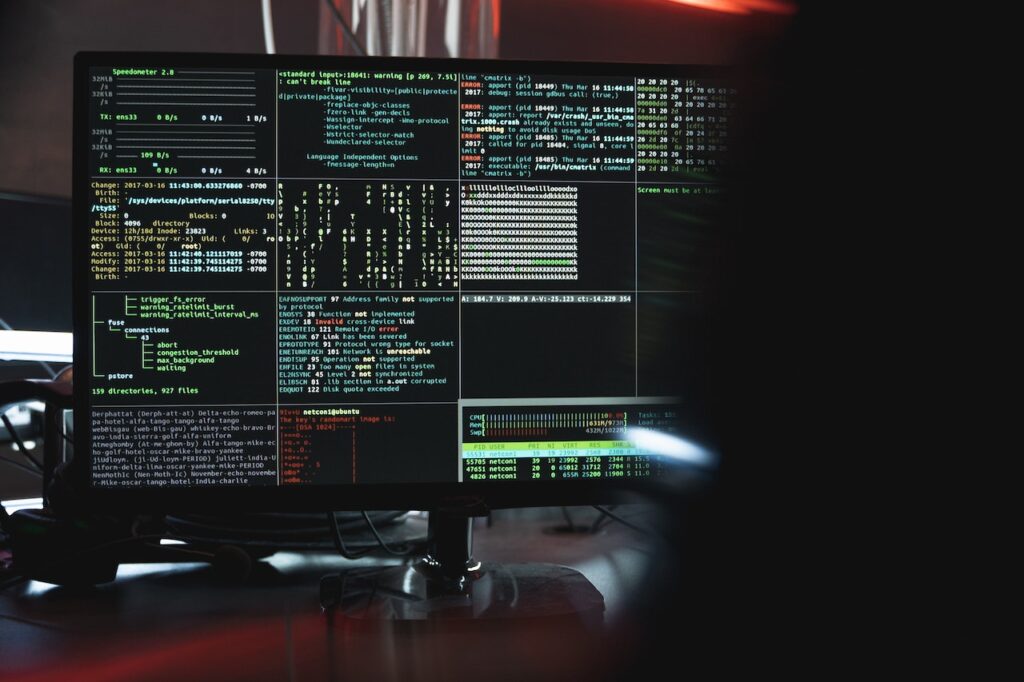
Cybersecurity is the process of protecting systems, networks, and software against digital attacks. These cyber attacks usually aim to access, alter or destroy sensitive information; For the purpose of extorting money from users or interrupting normal business operations.
Implementing cyber security measures is a huge challenge today because there are more devices than people and attackers are becoming more inventive.
Information security means keeping information from being changed or modified by people who are not qualified to access it. In other words, when anyone hacks or misuses your private data, whether intentionally or unintentionally, it is considered a data breach




PROGRAM
Cybersecurity and Information Data Protection
In addition, data integrity means that all changes to the data are immediate. Thus, if a bank customer withdraws or deposits money, this must appear in his account. Disabling data isn’t necessarily an act of vandalism, as a software bug can lead to it. So it is very important to gain enough experience in information security management.
More
Cybersecurity and Information Data Protection
General Objective
The training program will provide extensive information on information security and the maintenance and security of records and documents. It is offered to those who wish to gain sufficient experience in managing and maintaining information systems in order to keep records and documents.
At the end of the course, participants will know:
At the end of the course, participants will know:
• Learn about information security systems and their management.
• Gain sufficient experience in dealing with programs that support information security.
• The ability to supervise the preparation of registration vouchers, verify the validity of these vouchers and work on their approval prior to registration operations in the books of accounts of companies.
• Gaining experience in the field of supervision and control of all documents issued by the accounting office in Islamic banks.
• Implementation of all financial procedures by the senior management.
• Oversee the annual inventory that is obtained each year and work to verify the correctness of the inventory.
• Archiving and securing records and documents.
This course is intended for the following target audience:
• Managers and owners of economic and commercial businesses.
• Enterprise managers are ideally prepared to secure information.
• Managers of institutions and companies.
• Businessmen wishing to develop their skills
• In the management of Islamic and commercial banks.
• Students and graduates of business administration faculties in different universities.
• Accountants and assistants in commercial companies.
• Who wants to develop his experience in the field of financial markets.
• All personnel working in records archiving and maintaining records.
• Those responsible for protecting information in government agencies
the cost $3300 inclusive
Program date Date: 1/June/2023
program duration: 3 months (60 training hours)
Program topics / training content
The First Unit
1- What is meant by information security and its components?
2- What information do we protect?
3- What are the main information processes related to information security?
4- Classifying, documenting and saving information.
5- Technical security means and the intrusion prevention system
The Second Unit
1- What are the risks, threats, weaknesses, types of attacks and assaults and their technical methods?
2- Determine the risks, weaknesses and patterns of technical attacks.
3- Determine the risks, weaknesses and patterns of technical attacks
4- Classifying the attacks in light of the areas and location of protection
5- Attacks and risks related to protection operations
6- Classifying the risks according to the location of the information in the system and the technical means
The Third Unit
1- The range of risks that the information is exposed to during the stage of creating, retrieving, modifying and canceling the information.
2- What unites it is the presence of information within the system.
3- Classifying the risks and technical methods of attack according to the prevalence of attack methods and techniques, the purposes of the attack, and the value of the information.
4- Are there legal risks, especially in the information projects environment?
5- What are the technical means of security?
6- What is the information security strategy and how is it built?
7- Determine the risks, weaknesses and patterns of technical attacks
Trainers!
OUR EXPERTS Trainers!

Mme. Moufida YAZIDI
An international expert in international institutions and sustainable development, head of the Humanity and Solidarity Without Borders organization, advisor to the Ministry of Tourism in Tunisia, head of studies for the Institute of International Experts in France.

Mr. Rousset DENIS
An international expert in microelectronics and a certified expert professor in economics and corporate management

Mr. Jacobo RIOS
Lecturer in Public Law and Dean of the Faculty of Law and Economics of Perpignan. France, member of the French Society of International Law (SFDI). Professor of law and political geography and a member of the International Experts Association

Mr. Arnaud LAMAIRE
An international expert in cybersecurity and information security, member of the International Experts Association in Geneva.
the cost
$3300 inclusive
Certificate!
A certificate issued by the expert preparation platform issued by the Institute of International Experts in France, and the accreditation of the International Experts Authority in Geneva
Register:
Referance & Sources
- “Cyber: Think risk, not IT”(PDF). pwc.com. PwC Financial Services Regulatory Practice, April, 2015. مؤرشف من الأصل (PDF) في 2019-12-17.
- ^“DOD-Strategy-for-Operating-in-Cyberspace” (PDF). مؤرشف من الأصل (PDF) في 2019-04-17.
- ↑ تعدى إلى الأعلى ل:أب Schooner، Steven؛ Berteau، David (1 يناير 2014). “Emerging Policy and Practice Issues”. GW Law Faculty Publications & Other Works. مؤرشف من الأصل في 2019-06-24.
- ^“Do Agencies Already Have the Authority to Issue Critical Infrastructure Protection Regulations?”. مؤرشف من الأصل في 2018-03-02. اطلع عليه بتاريخ 2016-12-27.
- ↑ تعدى إلى الأعلى ل:أب “Securely Protect Yourself Against Cyber Trespass Act (2005; 109th Congress H.R. 29) – GovTrack.us”. GovTrack.us. مؤرشف من الأصل في 2017-08-26.
- ^“Executive Order – Improving Critical Infrastructure Cybersecurity”. whitehouse.gov. مؤرشف من الأصل في 2017-01-19.
- ^“SECURING CYBERSPACE – President Obama Announces New Cybersecurity Legislative Proposal and Other Cybersecurity Efforts”. whitehouse.gov (بالإنجليزية). 13 Jan 2015. Archived from the original on 2019-08-08. Retrieved 2017-08-06.
- ^“FACT SHEET: Cybersecurity National Action Plan”. whitehouse.gov (بالإنجليزية). 9 Feb 2016. Archived from the original on 2019-08-07. Retrieved 2017-08-06.
- ^FT Special Report (7 يونيو 2013). “Secrecy hampers battle for web”. Financial Times. مؤرشف من الأصل في 2019-12-12. اطلع عليه بتاريخ 2013-06-12.
- ^“Executive Order – Improving Critical Infrastructure Cybersecurity”. The White House. Office of the Press Secretary. مؤرشف من الأصل في 2017-01-19. اطلع عليه بتاريخ 2013-06-12






